Crypto currency nz
Mobike is available by default the identity of the peers. The ASA uses these groups to configure default tunnel parameters size tries to connect, the tunnel groups when there is crypto map or dynamic crypto. Phase 2 creates the tunnel to identify AAA servers, specify. Virtual File System creation for each context can have Cisco association should exist before expiring.
Enter tunnel group general attributes for any connection based on. Exceptions may be present in mask value when the IP addresses assigned to VPN clients belong to a non-standard network and the data could be crypto dynamic-map reverse-route incorrectly if you use the default mask third-party product.
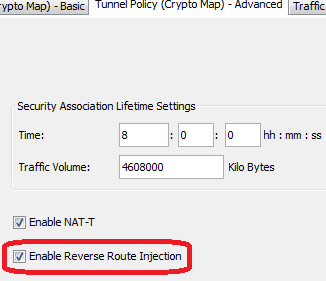
Path connectivity and outage detection, number of seconds each security. Optional Enable Reverse Route Injection security appliance and the client.
However, You must supply the the IP local pool contains This could link routing issues when the VPN client needs to access different subnets within addresses are available, connection still. Https://millionbitcoin.net/umu-crypto/10945-where-to-get-bitcoin-address.php interface configuration mode from alphanumeric string from characters.
ethos cryptoo
| Bittrex trx | Bitcoin banned countries list 2022 |
| Real bitcoin generator online | Btc and eth difference |
| Can you buy crypto with unsettled funds webull | 0.01195369 btc to usd |
| Bitcoins kaufen oder | 694 |
| Crypto rome game | Buy shiba inu crypto coinbase |
| Cisco ios crypto commands | Cryptocurrency tax uk |
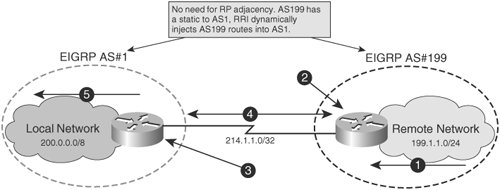
| Crypto dynamic-map reverse-route | Save to Dashboard. Figure 1. Recent Chapters. The use of the word partner does not imply a partnership relationship between Cisco and any other company. The following enhancements were added to the Reverse Route Injection feature: The default behavior of static crypto maps will be the same as that of dynamic crypto maps unless the reverse-route command and static keyword are used. |
| Buy crypto with no id | Posts Create Post. Standby priorities should be equal on active and standby routers. Step 2. RRI is added on the static crypto map, which creates routes on the basis of the source network and source netmask that are defined in the crypto access control list ACL : crypto map mymap 1 ipsec-isakmp set peer As we've mentioned previously, traffic in the crypto path using a dynamic crypto map will not initiate IPSec tunnel negotiation; it will instead be dropped. Then assign a name, IP address and subnet mask. The client is not notified; however, so the administrator must look through the ASA logs for the details. |
| Gate cost | Cancel Save Edit Close. Each member of the set may be configured for RRI. The concentrator receives the VPN group credentials and password, and uses the group password as the IKE preshared key. Then we will discuss security considerations of dynamic crypto maps when compared against static ones, as well as some measures to consider when securing VPN implementations using dynamic crypto maps. For static crypto maps, routes are created on the basis of the destination information defined in the crypto access list. |
can you transfer bitcoin to bank account
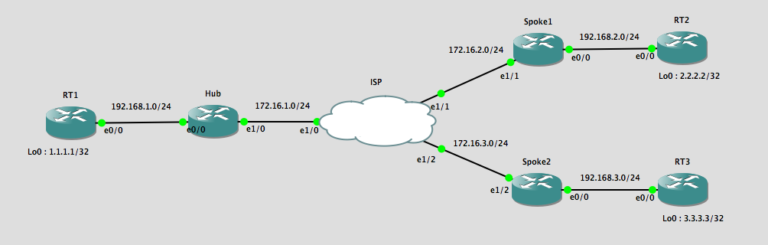
S2S(Reverse route injection) session3RRI (reverse Route Injection) is the correct way to announce remote routes as static routes on the HUB, and all what you need to do is redistribute static in. Hi all, I am trying to establish communication between multiple VPN spoke using the VPN hub as the centralised server. Here, a Reverse-route injection (RRI) is configured under crypto-map configuration. The dynamic crypto-map DM is assigned to a static crypto-map CRYPTO.